Modern computer hackers are usually defined as skilled programmers and computer experts who focus on software, computer and network vulnerabilities Almost every week mass media communicates about hackers having stolen thousands of passwords and other sensitive private information. It is commonplace to read articles about hackers having taken advantage of system vulnerabilities to bypass security barriers in order to fraudulently access private and company networks. The current understanding of the term ‘hacker’ is influenced by the news, and this twists the original definition of what a hacker is. Today’s perception of the term ‘hacker’ tends to be reduced to ‘black hat’ and ‘cyber-criminal’. This has not always been the case, and the term ‘hacker’ conveys a much broader meaning.
[Source: https://media.springernature.com/lw685/springer-static/image/chp%3A10.1007%2F978-3-030-29053-5_9/MediaObjects/466414_1_En_9_Fig3_HTML.png?as=webp]
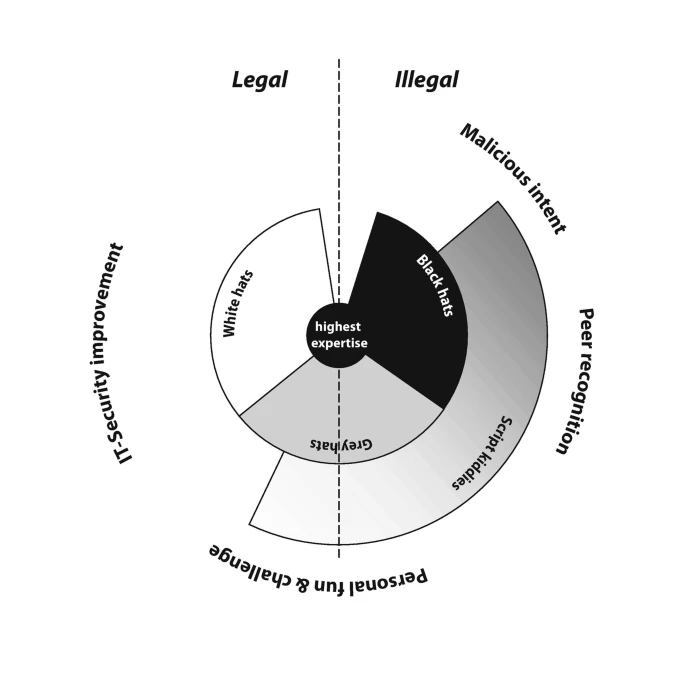
White hats, black hats, grey hats and script kiddies (Note that the outer layer refers to one predominant motivation. For example, not only grey hats, but also white hats as well as black hats may have fun in doing their activities or enjoy taking a challenge. White hats might also look for peer recognition)
Also known as “white hats,” ethical hackers are security experts that perform these security assessments. The proactive work they do helps to improve an organization’s security posture. With prior approval from the organization or owner of the IT asset, the mission of ethical hacking is opposite from malicious hacking. Ethical hackers use their knowledge to secure and improve the technology of organizations. They provide an essential service to these organizations by looking for vulnerabilities that can lead to a security breach. An ethical hacker reports the identified vulnerabilities to the organization. Additionally, they provide remediation advice. In many cases, with the organization’s consent, the ethical hacker performs a re-test to ensure the vulnerabilities are fully resolved. Malicious hackers intend to gain unauthorized access to a resource (the more sensitive the better) for financial gain or personal recognition. Some malicious hackers deface websites or crash backend servers for fun, reputation damage, or to cause financial loss. The methods used and vulnerabilities found remain unreported. They aren’t concerned with improving the organizations security posture.
REFERENCES
- https://blog.malwarebytes.com/101/2021/06/white-hat-black-hat-grey-hat-hackers-whats-the-difference/
Comments
Post a Comment